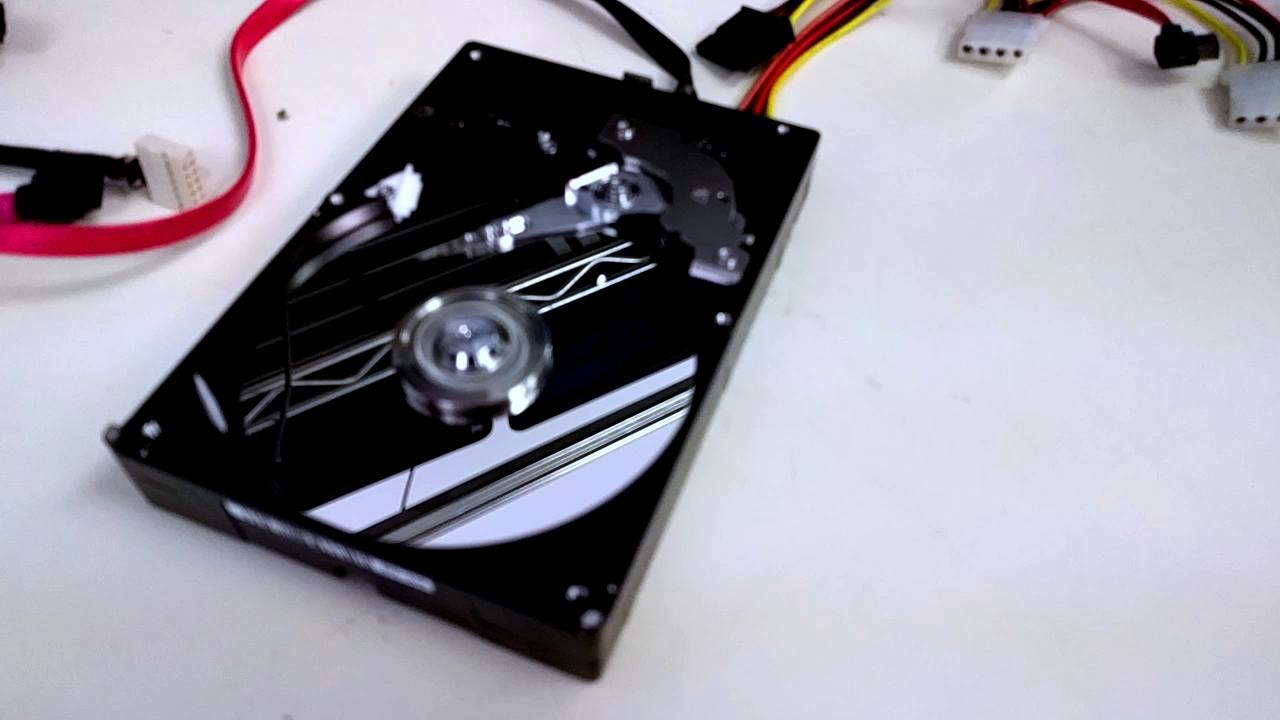
Data With a Drip
23 September 2022

Spotted in the lab. This one needed a bit of specific pre-recovery work.
Keeping Business Going When Extreme Weather Threatens Data
9 August 2022

The NOAA prediction of an above-normal Atlantic storm season seems to be staying on course but while extreme weather can be bad for digital devices it doesn’t have to mean a bad day for data. Forecasts are a good reminder of the precautions and prevention tips you can take to protect data and keep business going in the event of tough climate threats.
Sounds Like Something Is Wrong...
14 April 2022
Hard drive making weird noises suddenly? Watch a clip from the recovery lab and you be the judge.
Protecting Olympic Moments at the Beijing Winter Games
14 February 2022

Good luck to all the athletes competing at Beijing 2022. Protecting golden moments is what it’s all about when data loss is in play.
SUBSCRIBE
Get the Platter Chatter Digest in your inbox once in awhile with the latest posts. We’ll never spam you or sell your email address, and you can unsubscribe at any time.
