Keeping Business Going When Extreme Weather Threatens Data
9 August 2022

The NOAA prediction of an above-normal Atlantic storm season seems to be staying on course but while extreme weather can be bad for digital devices it doesn’t have to mean a bad day for data. Forecasts are a good reminder of the precautions and prevention tips you can take to protect data and keep business going in the event of tough climate threats.
Sounds Like Something Is Wrong...
14 April 2022
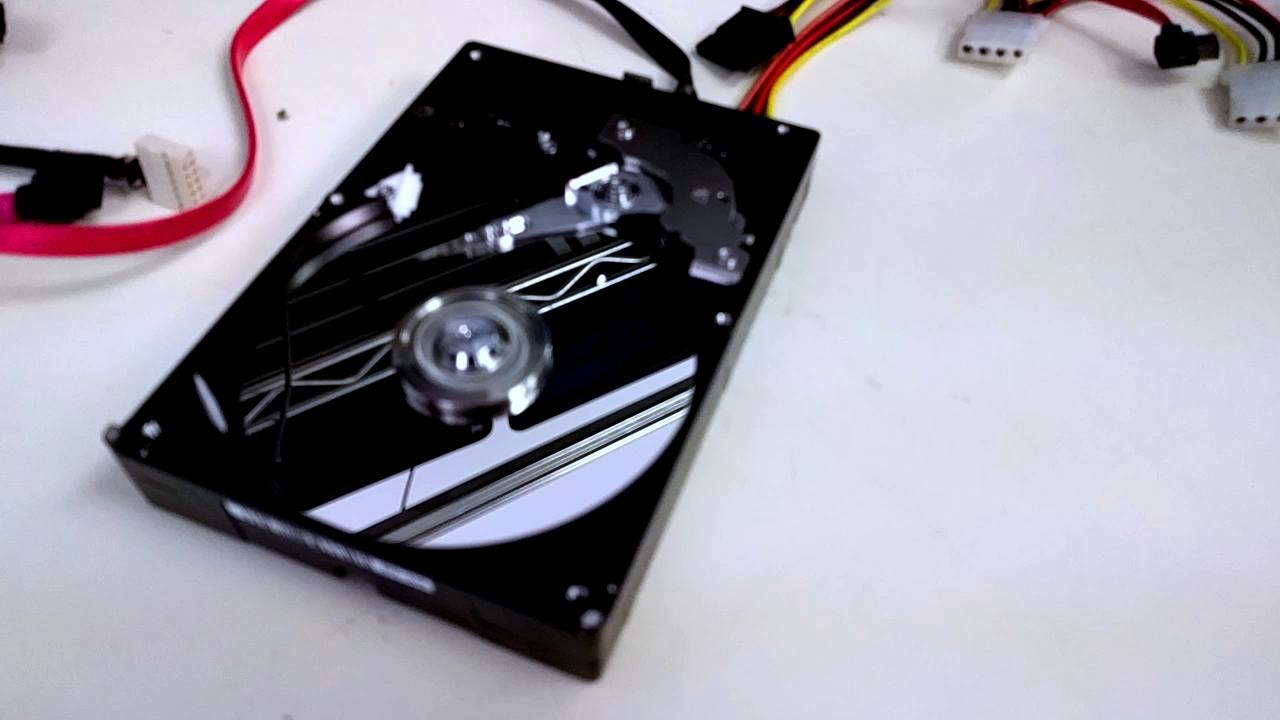
Hard drive making weird noises suddenly? Watch a clip from the recovery lab and you be the judge.
Interview: Tech Talk with Marc Saltzman, January 9th
12 January 2022

The first Tech Talk radio show of the year with Marc Saltzman featured a segment with CBL talking about dealing with data disasters, backup tips, data destruction and more.
The Grinch Wants Your Data: Holiday Shopping Do's & Don'ts
29 November 2021

Shopping of all sorts is making a comeback after the impacts of the COVID-19 pandemic and Black Friday and Cyber Monday remain at the center of the season. Being back in the habit is a blend of in-store and online shopping now. Where there are deals, there are cybersecurity threats. While more consumers are aware of the weaknesses and data breaches out there, the number of attack vectors out there continues to rise and hackers are there to take advantage. When you’re out and online looking for discounts and deals, protect yourself from Grinches that want to get ahold of your data with these tips.
SUBSCRIBE
Get the Platter Chatter Digest in your inbox once in awhile with the latest posts. We’ll never spam you or sell your email address, and you can unsubscribe at any time.
