Rise in Data Threats Adds to Coronavirus Crisis
22 April 2020
As the COVID-19 pandemic continues to challenge countries all over the world, data is playing an important role in the fight but is also under heightened risk from threats to cybersecurity and data safety.

Study: Wide Array of Private Data on Secondhand Drives, a Reminder to Discard With Discretion
15 October 2019
Researchers at the University of Hertfordshire performed a study examining secondhand hard disk drives and found they often contained data from their previous owners.

Art Exhibit Focuses on E-Waste Data Dangers
6 June 2018
A duo of artists known as KairUs curious about private data breaches and e-waste created an exhibition of artworks entitled “Forensic Fantasies”. Highlighting some key issues and effects related to e-waste dumps in places like Ghana, a topic we’ve covered before, they look at some interesting intersections of technology, the environment, and society.
![Chomping at the Bit[coin] to Acquire Cryptocurrency? Chomping at the Bit[coin] to Acquire Cryptocurrency?](https://www.cbldatarecovery.com/blog/images/153.jpg)
Chomping at the Bit[coin] to Acquire Cryptocurrency?
2 March 2018
The Truth Behind the Currency of the Internet
Before deciding to hop on the Bitcoin bandwagon, it’s important to fully understand the risks and implications of the unknown world of encryption keys, digital tax evasions, and Blockchain technology.

Loves Me, Loves Me Not: 4 Sweetheart Scams to Avoid This Valentine’s Day
13 February 2017
With Data Privacy Day and Safer Internet Day behind us and Valentine’s Day just ahead, it’s time to take what we learned and apply it.
The Rise of Ransomware: How to Handle Data Hijacking
16 May 2016
Ransomware is all the rage—and not in a good way. Cybersecurity experts are calling these virtual attacks an ‘epidemic’ of epic proportions.
In fact, its exponential growth over the past few years has left individuals, companies, and industries feeling both enraged and powerless.
Why? Well, because the only protection against ransomware is caution.

Spring Into Action: Top 5 Do's & Don'ts of Data Cleanup
19 April 2016

“April showers bring May flowers,” as they say. April also brings with it the frenzy of spring cleaning. This is the time of year when everything must sparkle, fit neatly into its predetermined spot, or go curbside. Everywhere and everything is fair game: your home, your garage, the interior and exterior of your car, your fridge, your office, and…your data.
Just like the clutter in your closet or garage, your data can be disorganized, old, poor quality, or redundant. Fortunately, de-cluttering your data will make your life (and business) run more smoothly in the long-term.

How to Demolish Old Hard Drive Data (keeping your data safe, the logical way)
24 March 2016

If you have a computer that you are getting rid of you need to take special care of the data you have stored inside it. Whatever information you have saved on the hard drive inside: photos, documents, financial files, passwords, emails — personal information, does not simply go away if you hit delete or drop stuff in the Recycle Bin.
Ben Popken at NBC did a video showing some low-tech solutions to this problem. He trashes hard drives with everything from hammers and baseball bats, to submerging in water and burning with fire. Watch the video after the jump.

Tips for Secure Online Shopping
9 December 2015

Increasingly more people are opting to do their holiday shopping online rather than subject themselves to the chaos of crowded malls this time of year. Saving people time and energy over the hectic holiday season is no doubt a great benefit brought by the evolution of the internet, but it doesn’t come without its own unique set of evils.
Recent incidents of cybersecurity and data theft have brought light to the risks consumers face when sharing and entrusting their sensitive data with corporations and third party institutions. Malicious intentioned cyber criminals continue to develop new, tech-savvy ways to hack into people’s private accounts for the purpose of stealing sensitive information.
Protect your data while doing your holiday shopping online this month with these tips and safety precautions.

Lessons on Data Safety from the Ashley Madison Hack
10 September 2015
 No matter what your stance on the Ashley Madison cyberattack or where your interest lies, there is one important lesson that everyone should be taking from the incident: your data is not as safe as you think it is. The apparent vulnerability of sensitive data submitted online is cause for alarm and serious consideration.
No matter what your stance on the Ashley Madison cyberattack or where your interest lies, there is one important lesson that everyone should be taking from the incident: your data is not as safe as you think it is. The apparent vulnerability of sensitive data submitted online is cause for alarm and serious consideration.

Data Safety on and off the Internet
9 February 2015
 If data safety was a coin, data protection would be one of the sides and the other would be data destruction. On Safer Internet Day, we’re thinking about how all of our data – information we create, information created about us, etc – relates to our safety.
If data safety was a coin, data protection would be one of the sides and the other would be data destruction. On Safer Internet Day, we’re thinking about how all of our data – information we create, information created about us, etc – relates to our safety.
EHR Data Safety Threat Is Real - Clerk Charged with Selling Patient Info
26 November 2014
In a rush to modernize and increase technological access sometimes the looming threats to privacy and safety of personal healthcare information are not given as much attention. A recent story exemplifies a growing real threat.

Data Safety Archive: Photocopiers Potential Security Risk
27 March 2013
 Ever thought about all the information that passes through your office copy machine? Here’s a good look at one place where the security of your personal information is threatened.
Ever thought about all the information that passes through your office copy machine? Here’s a good look at one place where the security of your personal information is threatened.
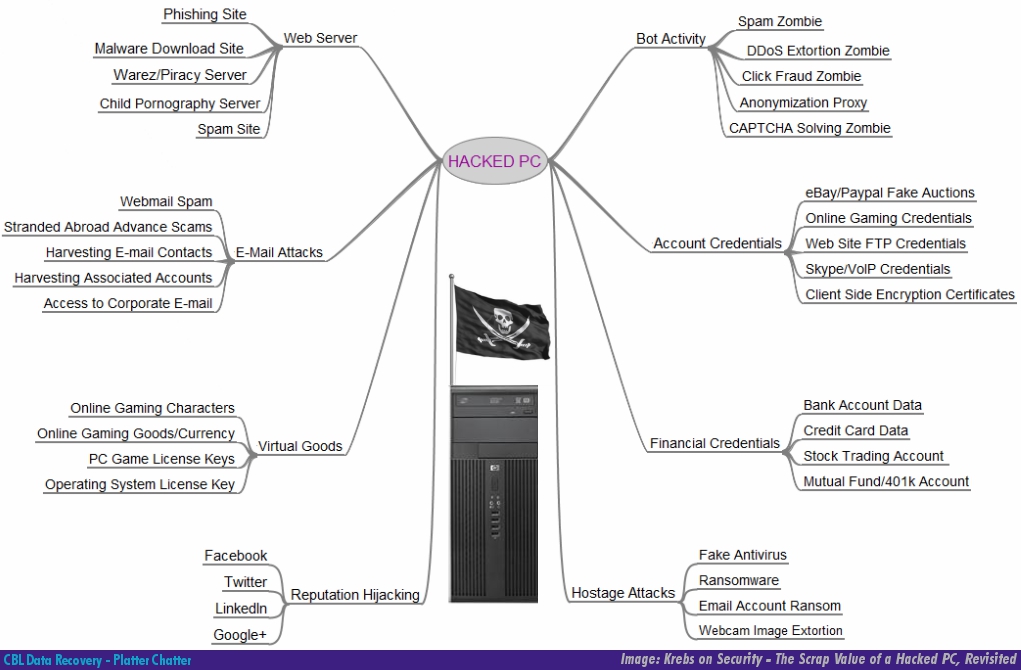
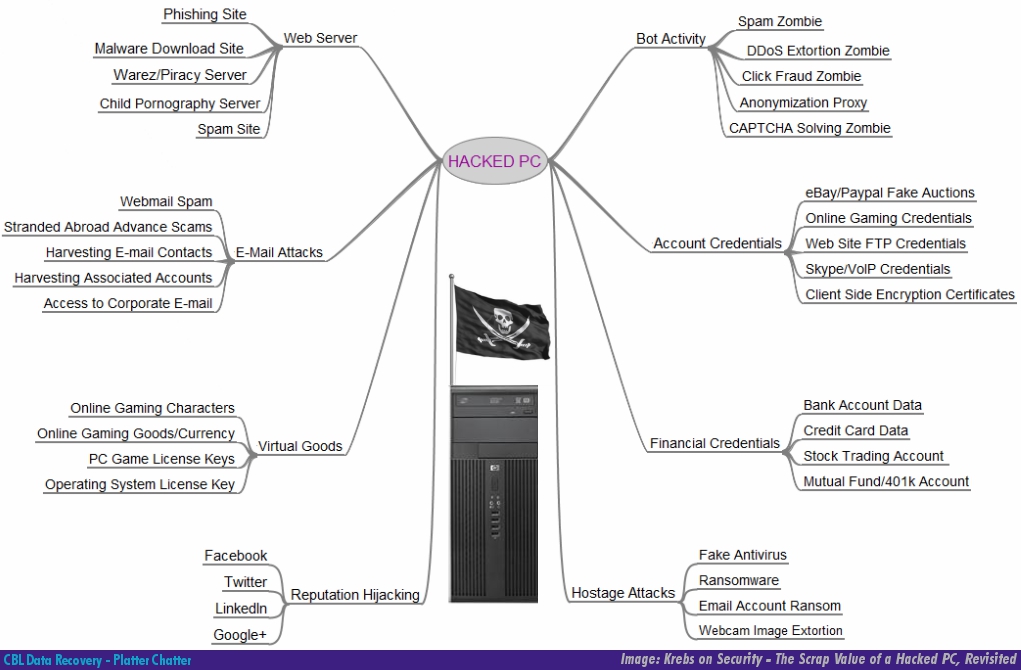
Data Safety: The Value of Your Data to a Hacker
18 October 2012
We’ve talked about data safety and protection before. Besides the destruction of information from crashes and deletion, threats to your data’s safety come in the form of threats to its security, and that affects your privacy.
Tech columnist Brian Krebs has a great article where he tries to tackle the challenge of explaining why a hacker would want to get into your PC. What’s interesting is that most of the items listed are some sort of data or personal information.