June 25
Last updated: June 30th, 15:45 EDT
That connected NAS storage device you’ve had plugged in since 2015 may just be a sitting duck to unexpected data loss from a vulnerability that allows a reset function to be triggered. The Internet of Things convenience of connected devices is looking like anything but for users that reported missing data on a support forum this week. Western Digital, major storage manufacturer and maker of the external hard drive line that includes the My Book Live, issued a recommendation that owners unplug their devices from the internet until further notice while they investigate. Details about how this could happen and glimmers of hope for the rapidly rising number of users affected that their suddenly erased data could be recovered are only just starting to be pieced together.
Compromised by Connectivity
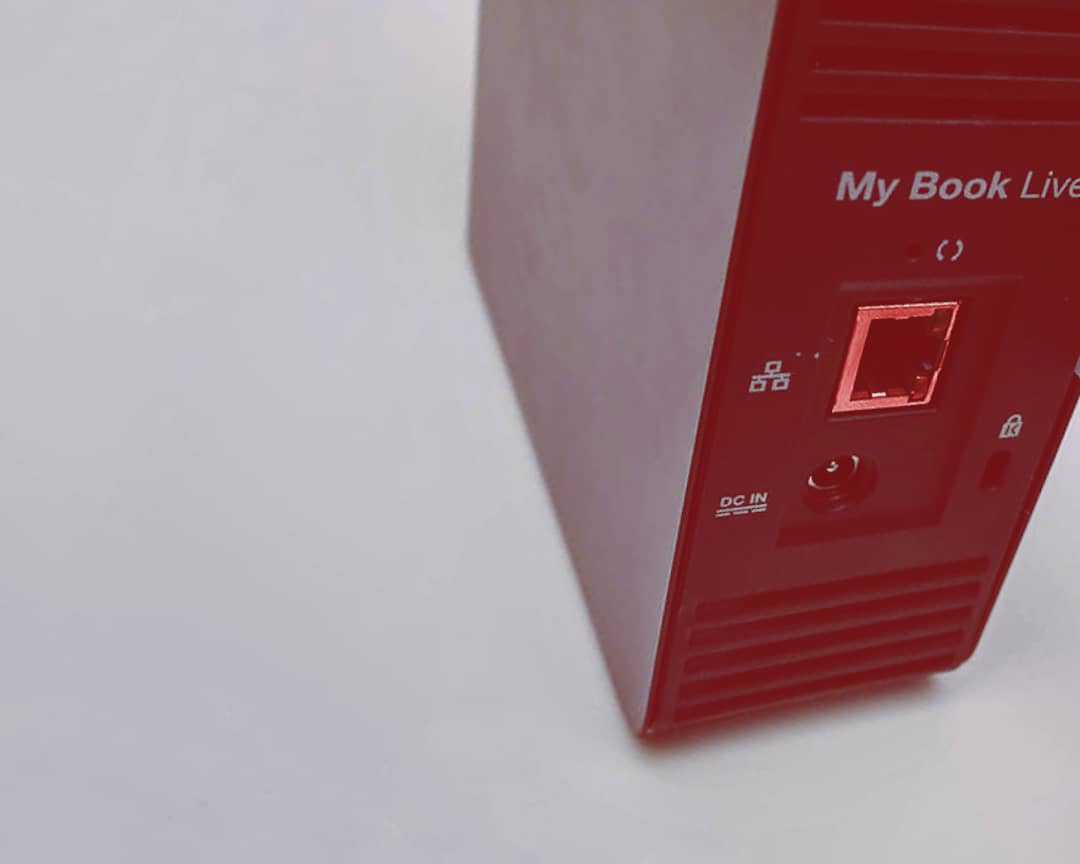
From an officially posted advisory, WD shared preliminary findings into how the external hard drives may be compromised and left one recommended action: unplug! The vulnerability that causes the drives to be compromised is what's known as a "remote command execution" bug. The National Institute of Standards and Technology (NIST) keeps a database of these and lists CVE-2018-18472 as a vulnerability that can be "triggered by anyone who knows the IP address of the affected device". NAS devices such as this connect via USB cable to local computers but also utilize a network port to provide functionality such as making data accessible across network and also firmware updates from external sources. In devices like this a commonly used protocol uPnP(Universal Plug-and-Play) is also enabled on many people's routers to allow devices to easily be accessed and configured over the network. The remote execution described by the vulnerability report means that an unsuspecting device may be connected to and issued commands to manipulate data without authorization or knowledge of the owner. As the compromise is triggered from online connectivity WD's only recommendation for the time being is to disconnect the device from the internet.
Reports from numerous people on the support forums describe a pretty alarming data loss situation that seems to come from a factory reset on their My Book device. Users report logging on to their drive to find a message about a ‘factory reset’ being engaged without their input. Some adventurous owners have checked logs on devices that appear to show unauthorized connections to their devices and one single command executing a factory reset script. No one is happy to have all their files, ranging from documents and photos to business record backups, wiped out as a result of an unplanned reset.
In some intrepid reporting, Dan Goodin at Ars Technica outlined how a factory reset could possibly be done without any permission. Usually that kind of operation on a device would require some authentication, but analysis of the PHP script that does the reset shows the code has a commented out portion that appears to be the check for valid credentials! Not a good look for Western Digital, and not a good situation for owners as it appears this vulnerability existed ahead of the execution attack and is more likely the key to getting everyone into this mess of being exploited in the first place.
It’s not clear who would be performing the malicious action but Western Digital does not believe it is coming from their cloud servers in any way at this time but rather a device exposed to the public internet being taken advantage of. In the most recent updates it is theorized that multiple attackers may be competing via the multiple vulnerabilities to take control of the devices from each other. Even with private LAN and router configurations protecting devices, the vulnerability is such that a device can be compromised regardless because of the update features and uPnP access. This is perhaps a reminder of the dangers of devices connected to the internet with little interaction, the so-called Internet of Things. To add to a troubling situation on June 25th WD added information that some log file reports show evidence that attackers transferred a trojan horse virus file to the compromised devices in the form of a Linux formatted executable binary file. This has been reported to virus databases so scans will pick up the dangerous files in future also. The My Book Live product isn’t being sold anymore either. In fact, the last firmware update on the device was 2015. While the vulnerability was reported in 2018, the unfortunate age of the devices means Western Digital claimed at the time it was beyond their “software device support lifecycle”. As the reports mount (the complaints only really started June 24th) owners suffering from a compromised My Book Live factory reset are finding little comfort.
Chance for Recovery
As with any data loss emergency, CBL is receiving inquiries from users looking for a glimmer of recovery hope. The extent of the damage caused by the exploited vulnerability is still being determined in the wild. Due to the nature of how a device performs the factory reset command, filesystem recovery may be possible.
Our recommendations for how to tackle the situation is to first follow the WD advice and unplug your My Book Live (or Live Duo) from the internet. If you think you’ve been compromised or notice a device has been reset, some of our standard recommendations can go a long way to increasing your chances for an successful data recovery.
- Don’t panic! Do not assume files on the device are lost.
- Turn off the device. Avoid repeated resets and power-cycling.
- Do not attempt to open the external housing or repair a drive yourself.
- Contact a recovery specialist and send your device to a lab for an evaluation. Let the experts assess and determine a recovery solution if needed.
We’ll update this blog post as more details surface about owners’ experiences with this vulnerability and our own findings.
Update from WD on support for compromised drives
Update provided late June 29th
For customers who have lost data as a result of these attacks, Western Digital will provide data recovery services. My Book Live users will also be offered a trade-in program to upgrade to a supported My Cloud device. Both programs will be available beginning in July, and details on how to take advantage of these programs will be made available in a separate announcement.
Sources/Further Reading
- “I’m totally screwed.” WD My Book Live users wake up to find their data deleted
- WizCase Report: Vulnerabilities found on WD My Book, NetGear Stora, SeaGate Home, Medion LifeCloud NAS
- WDC-21008: Recommended Security Measures for WD My Book Live and WD My Book Live Duo
- NVD – CVE-2018-18472
- Pull your Western Digital My Book Live NAS off the internet now if you value your files
- VirusTotal database entry for preliminary trojan horse analysis
- Hackers exploited 0-day, not 2018 bug, to mass-wipe My Book Live devices
Category: data loss prevention
Tags: cybersecurity, data security, external hard drive, internet of things, western digital, wiping
Jun 30, 05:19 PM
WB has a BIG lawsuit coming and they are trying to get people to take the replacement drives if they agree not to sue them!