
Equifax: Zero Credit for Poor Handling of Massive Data Breach
Sep 26
“Based on the information provided, we believe that your personal information may have been impacted by this incident.”
Sound familiar? You and 143 million other people in the United States, the UK, and Canada.That’s right – Americans weren’t the only ones affected by the massive Equifax data breach.
It’s been quite a year for data breaches (many a result of escalating and evolving ransomware), but this situation was largely precipitated by Equifax’s negligence. Companies who feel they are taking extensive preventative measures can always do more. Being on the defense is not the same as mounting an offense.

Back-to-School, Back to Secure: Security Best Practices for All Age Groups
Aug 17
Whether it’s coming to a grinding halt or a gradual slowdown, there’s no doubt about it: summer is approaching its end. But while the temperatures are decreasing, hackers are increasing their efforts targeting networks and users of all ages. Cyberattacks span payment card fraud, unintended disclosure, hacking, malware, insider leaks, and ransomware—these are only a few of the most common approaches.
Different age groups vary in online behavior and thus, are susceptible to different online scams, threats, and pitfalls. Understanding risk factors is the first step toward protecting yourself.

Amazon Goes Grocery Shopping, Buys Whole Foods
Jun 23
More and more, businesses are looking for ways to blend brick-and-mortar stores with online services. The company that rules the online marketplace? Amazon. But Bezos is branching out.

Pokémon No-Go: What’s the Catch?
Jul 15
The mobile app, Pokémon Go, is a global phenomenon.
 Comfortably seated at No. 1 on mobile download charts for both iOS and Android users, the app has made virtual reality mainstream, prompting users to get off the couch and go explore the real world, but through a virtual lens.
Comfortably seated at No. 1 on mobile download charts for both iOS and Android users, the app has made virtual reality mainstream, prompting users to get off the couch and go explore the real world, but through a virtual lens.
However, people can collect a lot more than Pokémon.
We break down the basics of the game and look into some potential risks and threats to your data privacy, cybersecurity and more.

Data Safety Archive: Photocopiers Potential Security Risk
Mar 27
 Ever thought about all the information that passes through your office copy machine? Here’s a good look at one place where the security of your personal information is threatened.
Ever thought about all the information that passes through your office copy machine? Here’s a good look at one place where the security of your personal information is threatened.
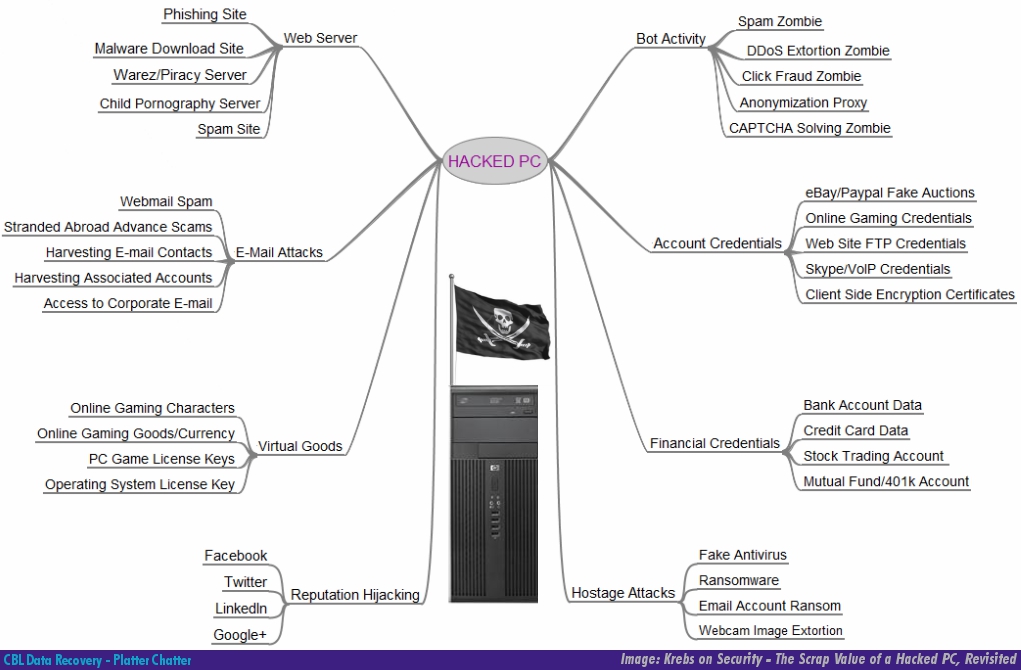
Data Safety: The Value of Your Data to a Hacker
Oct 18
We’ve talked about data safety and protection before. Besides the destruction of information from crashes and deletion, threats to your data’s safety come in the form of threats to its security, and that affects your privacy.
Tech columnist Brian Krebs has a great article where he tries to tackle the challenge of explaining why a hacker would want to get into your PC. What’s interesting is that most of the items listed are some sort of data or personal information.
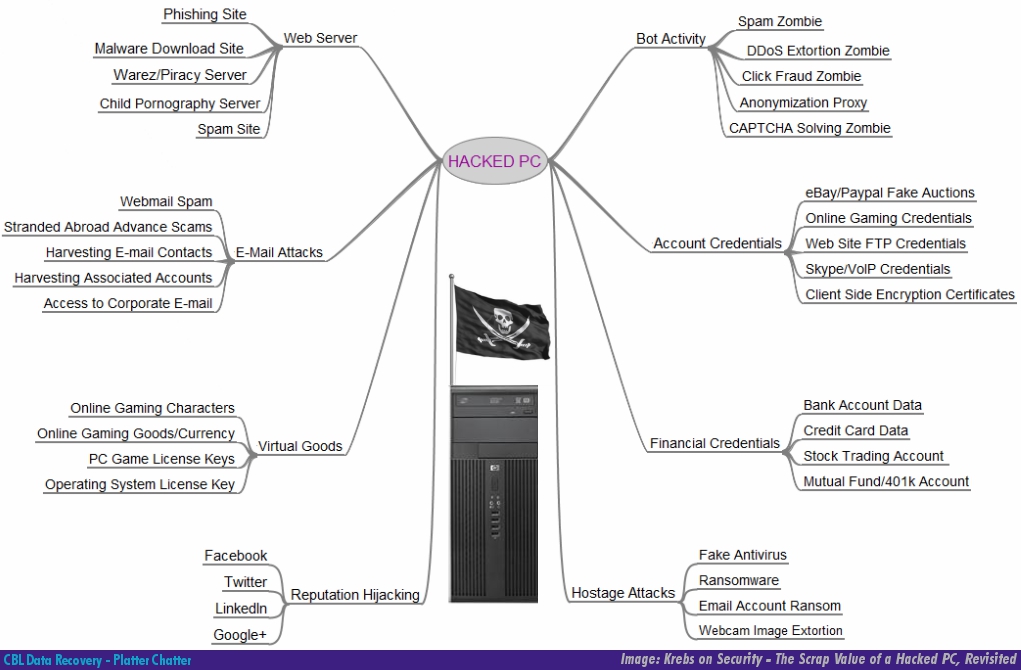
Clip: CBL Data Shredder - Costco Tech Connection
Feb 8
 The only thing we love almost as much as getting back our customers’ data is preventing it from falling into the wrong hands. The privacy of your information and importance of protecting data is a crucial part of what we do and of our digital society today. Getting rid of old hardware is one challenge, but what about the files and data stored on computers? Friend of Platter Chatter and tech reporter extraordinaire, Marc Saltzman, recently highlighted some key points about safely deleting data in Costco Connection magazine.
The only thing we love almost as much as getting back our customers’ data is preventing it from falling into the wrong hands. The privacy of your information and importance of protecting data is a crucial part of what we do and of our digital society today. Getting rid of old hardware is one challenge, but what about the files and data stored on computers? Friend of Platter Chatter and tech reporter extraordinaire, Marc Saltzman, recently highlighted some key points about safely deleting data in Costco Connection magazine.

Can you trust data recovery service providers?
Jan 17
 The worst has happened: the computer or server with your confidential and time-sensitive data has crashed. Panic starts to set in, and a quick call or visit to your IT support confirms that this issue is beyond the scope of your help desk’s services. It’s time to call in a data recovery provider. IT support probably already has a provider in mind. But what exactly are they going to do with your data? How can you trust them?
The worst has happened: the computer or server with your confidential and time-sensitive data has crashed. Panic starts to set in, and a quick call or visit to your IT support confirms that this issue is beyond the scope of your help desk’s services. It’s time to call in a data recovery provider. IT support probably already has a provider in mind. But what exactly are they going to do with your data? How can you trust them?

Canadian Privacy audit finds breach at Staples: laptops resold with customer data
Jun 21
Staples Business Depot, the office supplies store chain, was fingered by the office of Canada’s Privacy Commissioner in a recent report. The report details findings that Staples was reselling returned laptops and digital devices without properly wiping customer data off them.

New Jersey Hard Drive Data Security Breach A Reminder to Us All
Mar 11
 When the State of New Jersey was preparing to put a bunch of old computer equpiment up for auction to the public, it didn’t realize it was about to auction off the private data of members of that public. State Comptroller Matthew Boxer was reviewing the sale of hundreds of computers that is a usual occurrence in the state office when he discovered that the “hard drives in 79% of the machines had tons of private data on them” still! The sale was stopped thanks to the auditor’s investigation, but there is little doubt that the state had already been selling computers with confidential data on them for some time.
When the State of New Jersey was preparing to put a bunch of old computer equpiment up for auction to the public, it didn’t realize it was about to auction off the private data of members of that public. State Comptroller Matthew Boxer was reviewing the sale of hundreds of computers that is a usual occurrence in the state office when he discovered that the “hard drives in 79% of the machines had tons of private data on them” still! The sale was stopped thanks to the auditor’s investigation, but there is little doubt that the state had already been selling computers with confidential data on them for some time.

Your Privacy: How Safe Is Your Data? (Part 5)
Feb 15
 While the cost of a new computer or laptop continues to fall, we truly are almost in an age when these former room-sized giants are now disposable. When last year’s speed-demon is today’s dinosaur, and the cost and hassle of upgrading and updating is on par with simply buying new, what happens to your beloved old digital friend?
While the cost of a new computer or laptop continues to fall, we truly are almost in an age when these former room-sized giants are now disposable. When last year’s speed-demon is today’s dinosaur, and the cost and hassle of upgrading and updating is on par with simply buying new, what happens to your beloved old digital friend?
(Part 5 of our series on Data Safety)
Worrying About Your Data
Aug 18
More and more computer users are becoming aware of a growing amount of data privacy issues around us. Protecting your personal data should be a top priority given the alarming increase in identity theft. This is leading people to worrying about what happens to their personal information and who’s hands it can fall into. CBL offers some tips and options for securely disposing of old storage devices.