
The ABC’s of Cybersecurity
May 30
Not so long ago we were all anxiously biting our nails over the impending threat of the WannaCry cyberattack, which affected over 300,000 computers worldwide. Even though the ransomware attack was resolved in a matter of days, it swiftly incurred billions of dollars in damages. The reality is, it hasn’t been too long since this major attack, and threats to your own cybersecurity measures are as prevalent now as they were then. It’s important to take precautions when it comes to protecting confidential corporate information, but just what do those precautions entail?
WannaCrypt: The Ransomware That Makes You Wanna Cry
May 19
Ransomware isn’t new, but it’s been all over the news recently. Just last weekend, hackers launched a massive cyberattack that crippled hundreds of thousands of computers around the globe. Known as WannaCrypt—also called WannaCry or Wanna Decryptor—it is a particularly damaging brand of virus known as ransomware.

Data Safety on and off the Internet
Feb 9
 If data safety was a coin, data protection would be one of the sides and the other would be data destruction. On Safer Internet Day, we’re thinking about how all of our data – information we create, information created about us, etc – relates to our safety.
If data safety was a coin, data protection would be one of the sides and the other would be data destruction. On Safer Internet Day, we’re thinking about how all of our data – information we create, information created about us, etc – relates to our safety.

Digital Universe of Data Continues to Grow
Apr 28
The IDC is in with their latest report on the ever-expanding ‘Digital Universe’. Latest figures highlight that the world’s data is up to a staggering 4.4 ZETTAbytes.


Data Safety Archive: Photocopiers Potential Security Risk
Mar 27
 Ever thought about all the information that passes through your office copy machine? Here’s a good look at one place where the security of your personal information is threatened.
Ever thought about all the information that passes through your office copy machine? Here’s a good look at one place where the security of your personal information is threatened.
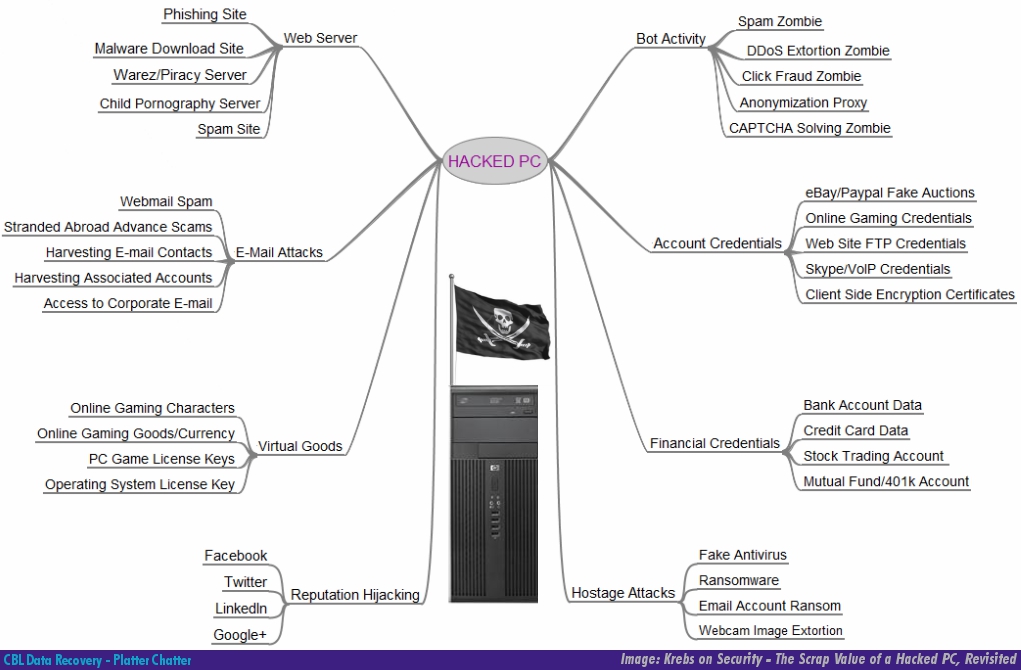
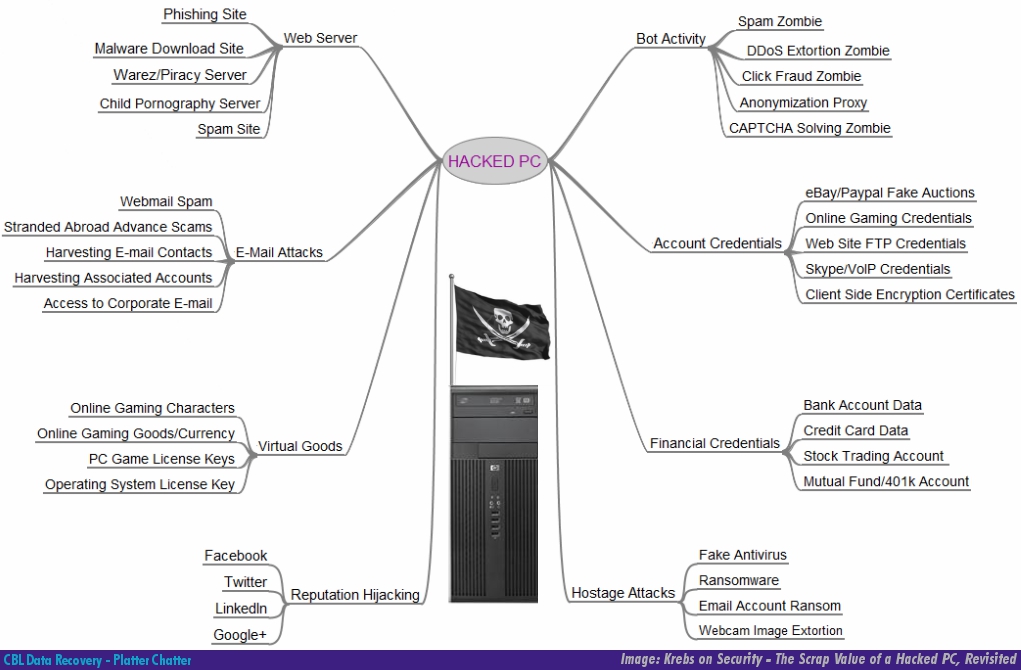
Data Safety: The Value of Your Data to a Hacker
Oct 18
We’ve talked about data safety and protection before. Besides the destruction of information from crashes and deletion, threats to your data’s safety come in the form of threats to its security, and that affects your privacy.
Tech columnist Brian Krebs has a great article where he tries to tackle the challenge of explaining why a hacker would want to get into your PC. What’s interesting is that most of the items listed are some sort of data or personal information.

Canadian Privacy audit finds breach at Staples: laptops resold with customer data
Jun 21
Staples Business Depot, the office supplies store chain, was fingered by the office of Canada’s Privacy Commissioner in a recent report. The report details findings that Staples was reselling returned laptops and digital devices without properly wiping customer data off them.

New Jersey Hard Drive Data Security Breach A Reminder to Us All
Mar 11
 When the State of New Jersey was preparing to put a bunch of old computer equpiment up for auction to the public, it didn’t realize it was about to auction off the private data of members of that public. State Comptroller Matthew Boxer was reviewing the sale of hundreds of computers that is a usual occurrence in the state office when he discovered that the “hard drives in 79% of the machines had tons of private data on them” still! The sale was stopped thanks to the auditor’s investigation, but there is little doubt that the state had already been selling computers with confidential data on them for some time.
When the State of New Jersey was preparing to put a bunch of old computer equpiment up for auction to the public, it didn’t realize it was about to auction off the private data of members of that public. State Comptroller Matthew Boxer was reviewing the sale of hundreds of computers that is a usual occurrence in the state office when he discovered that the “hard drives in 79% of the machines had tons of private data on them” still! The sale was stopped thanks to the auditor’s investigation, but there is little doubt that the state had already been selling computers with confidential data on them for some time.

Your Privacy: How Safe Is Your Data? (Part 5)
Feb 15
 While the cost of a new computer or laptop continues to fall, we truly are almost in an age when these former room-sized giants are now disposable. When last year’s speed-demon is today’s dinosaur, and the cost and hassle of upgrading and updating is on par with simply buying new, what happens to your beloved old digital friend?
While the cost of a new computer or laptop continues to fall, we truly are almost in an age when these former room-sized giants are now disposable. When last year’s speed-demon is today’s dinosaur, and the cost and hassle of upgrading and updating is on par with simply buying new, what happens to your beloved old digital friend?
(Part 5 of our series on Data Safety)

Protecting Backups: How Safe Is Your Data? (Part 4)
Feb 1
 Configuration of RAID arrays have been greatly simplified over the years. However, as we like to say, It’s Not A Matter of If, but When…. There are important details to remember when storing your data this way: even a RAID can fail.
Configuration of RAID arrays have been greatly simplified over the years. However, as we like to say, It’s Not A Matter of If, but When…. There are important details to remember when storing your data this way: even a RAID can fail.
(Part 4 of our series on Data Safety)

Protecting Backups: How Safe Is Your Data? (Part 3)
Jan 27
 Ensuring the protection of your data is just as important as the process of backing up your data in the first place. Making backups is certainly better than not making backups, but there are a few more steps you should consider to make sure that during emergencies your backup will get you up and running quickly.
Ensuring the protection of your data is just as important as the process of backing up your data in the first place. Making backups is certainly better than not making backups, but there are a few more steps you should consider to make sure that during emergencies your backup will get you up and running quickly.
(Part 3 of our series on Data Safety)

Your Backup: How Safe Is Your Data? (Part 2)
Oct 25
One day I’ll back up my data. One day.
“One Day” is here, mostly.
A variety of online backup services offer desktop-syncing programs to provide automatic backups of specific folders or files.
(Part 2 of our series on Data Safety)

Your Backup: How Safe Is Your Data?
Oct 21
 If data safety was a coin, data protection would be one of the sides (the other being data destruction). For most of us, backing up is an arduous process we know we need to do, but it’s historically been such a headache that it goes onto the “one of these days” list.
If data safety was a coin, data protection would be one of the sides (the other being data destruction). For most of us, backing up is an arduous process we know we need to do, but it’s historically been such a headache that it goes onto the “one of these days” list.
Broken Server + CBL = Disaster Relief
May 12
If you are an CIO you understand the importance of protecting corporate data. There is no magic formula for safeguarding vital information but certain steps can be taken. Many businesses have systems in place, backup redundancy, or hard drives upon hard drives — but how many are 100% confident those measures will hold up when the time comes?
Holiday Gift Idea for the Tech Savvy Person on Your List
Nov 13
Looking for a unique gift for the geek or nerd in your family?
At a loss as to what to buy a tech savvy friend this holiday season? You know the guy or gal who owns a couple of computers and is always being called upon to take...
Back to School Advice for Parents (and Students with Laptops, too)
Aug 20
In today’s world of e-gadgets, a new or used laptop or personal computer may also be on the Back-to-School shopping list.
Here’s some advice for parents.
Will the Summer of 2007 Damage Your Data?
Jun 29
Residents of some cities are already hearing and reading pleas from municipal officials restrict water consumption and to reduce their power consumption and the summer of 2007 is only one week old. Blackouts and brownouts have already occurred as air conditioners and fans are working overtime to keep workers...