
3 Things Driving Data in 2024
Feb 2
In 2024, data trends are being driven by our creation, capacity to store, and the challenges of protecting it. Here’s a breakdown of those 3 key areas to watch this year in storage tech and data use.

Machine Learning Makes Massive Black Hole Data Darker
May 3
The first-ever image of a black hole was captured by the Event Horizon Telescope team in 2019. It required a lot of observation data and processing. Researchers have now produced a finer image using even more data from a new source: models generated using machine-learning.
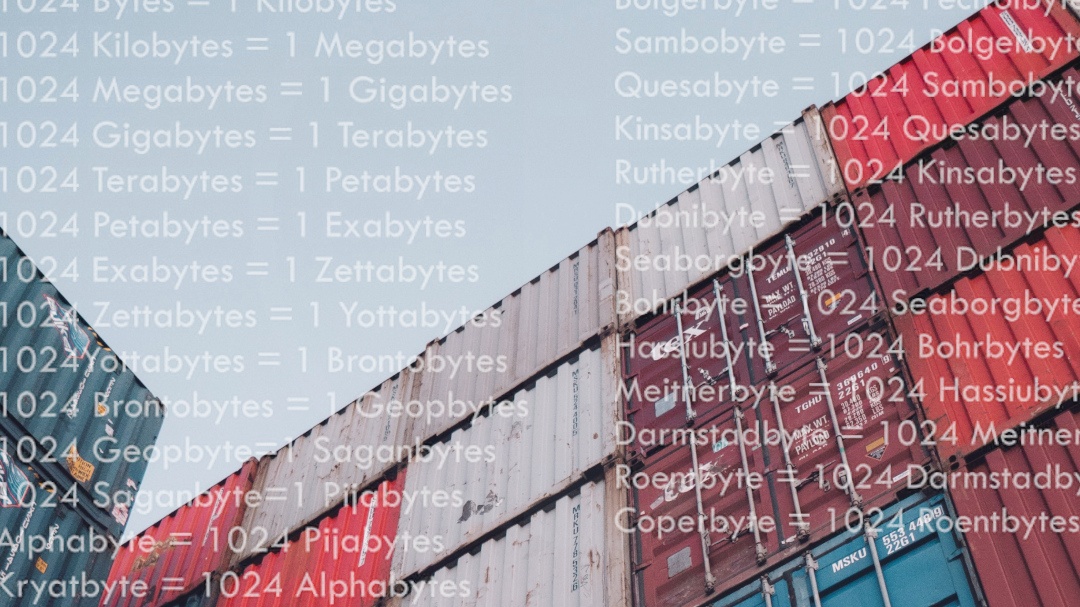
Beyond Bytes: Updated Unit Names Needed for Massive Digital Data
Nov 30
Gigabytes…Terabytes…Petabytes…Zettabytes… Naming units of computer memory follows a standard system of prefixes but after a certain range gets a bit informal. The common and even very large volumes we see in our digital landscape were covered for years. Until now. For the first time in 31 years the International System of Units (SI) has been expanded to include two more prefixes.

Behind the Big Data: Revealing Our Galaxy's Black Hole
May 18
Astronomers from the Event Horizon Telescope project revealed the first-ever image of the black hole that sits at the center of our galaxy known as Sagittarius A*. It was produced using observation data collected from the network of telescopes situated around the globe. How much data must you compute to get an image of an object that’s 27,000 light-years away, is 4 millions times more massive than our Sun, from a network of telescopes that make a dish the size of the Earth?

How Do You Pronounce Data?
Nov 19
After watching a handy pronunciation guide video we pondered our own preferences around the office & lab in how to say the word ‘data’. A Star Trek friend also weighed in.
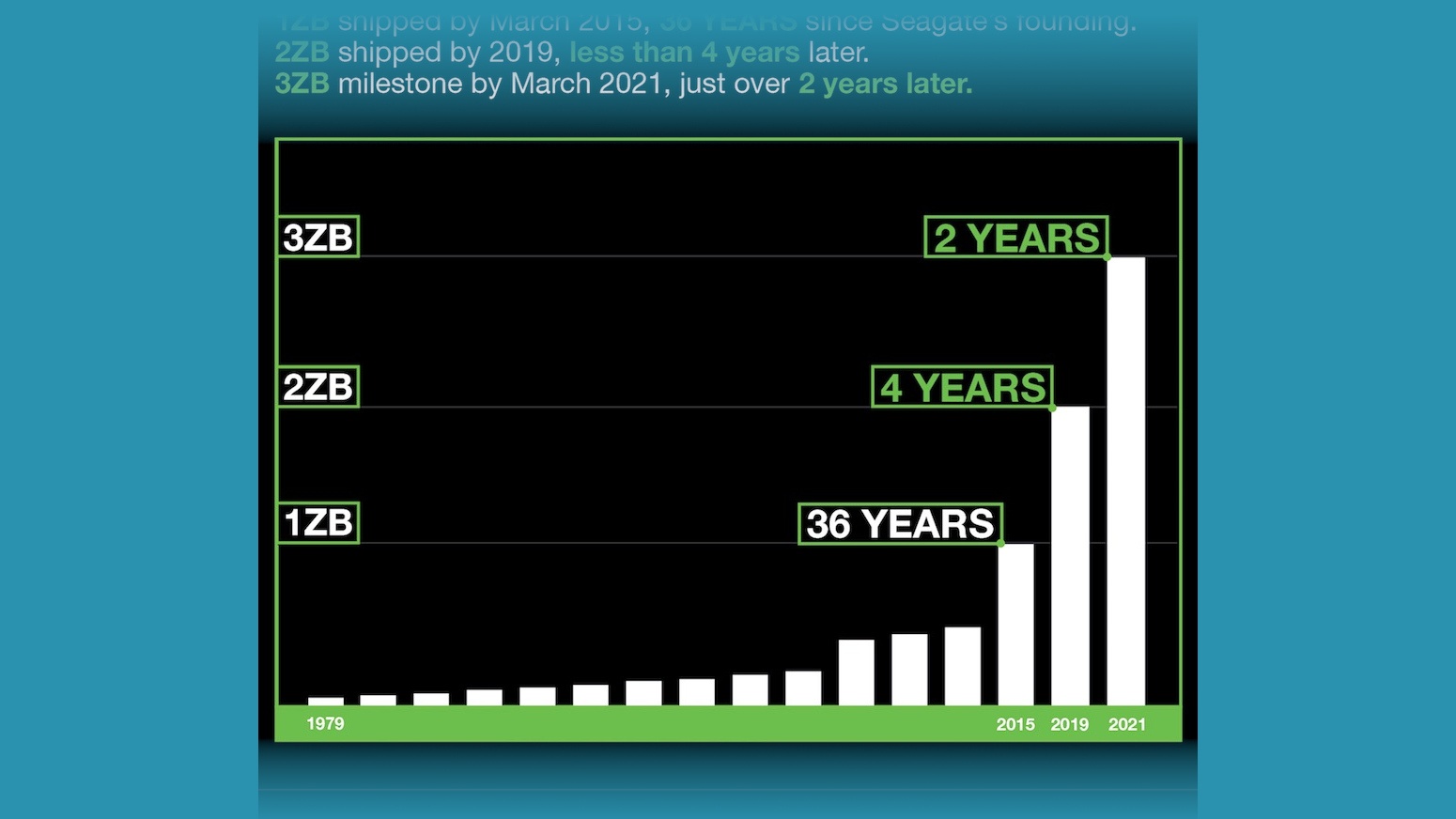
Shipping Capacity: Seagate reports 3 Zettabyte Storage Milestone
Apr 7
As creation and consumption of data continues to grow like never before, the storage giant claimed it has now shipped over three zettabytes of drive storage capacity, highlighting again how the amount of data in the digital world is not only climbing, but accelerating.
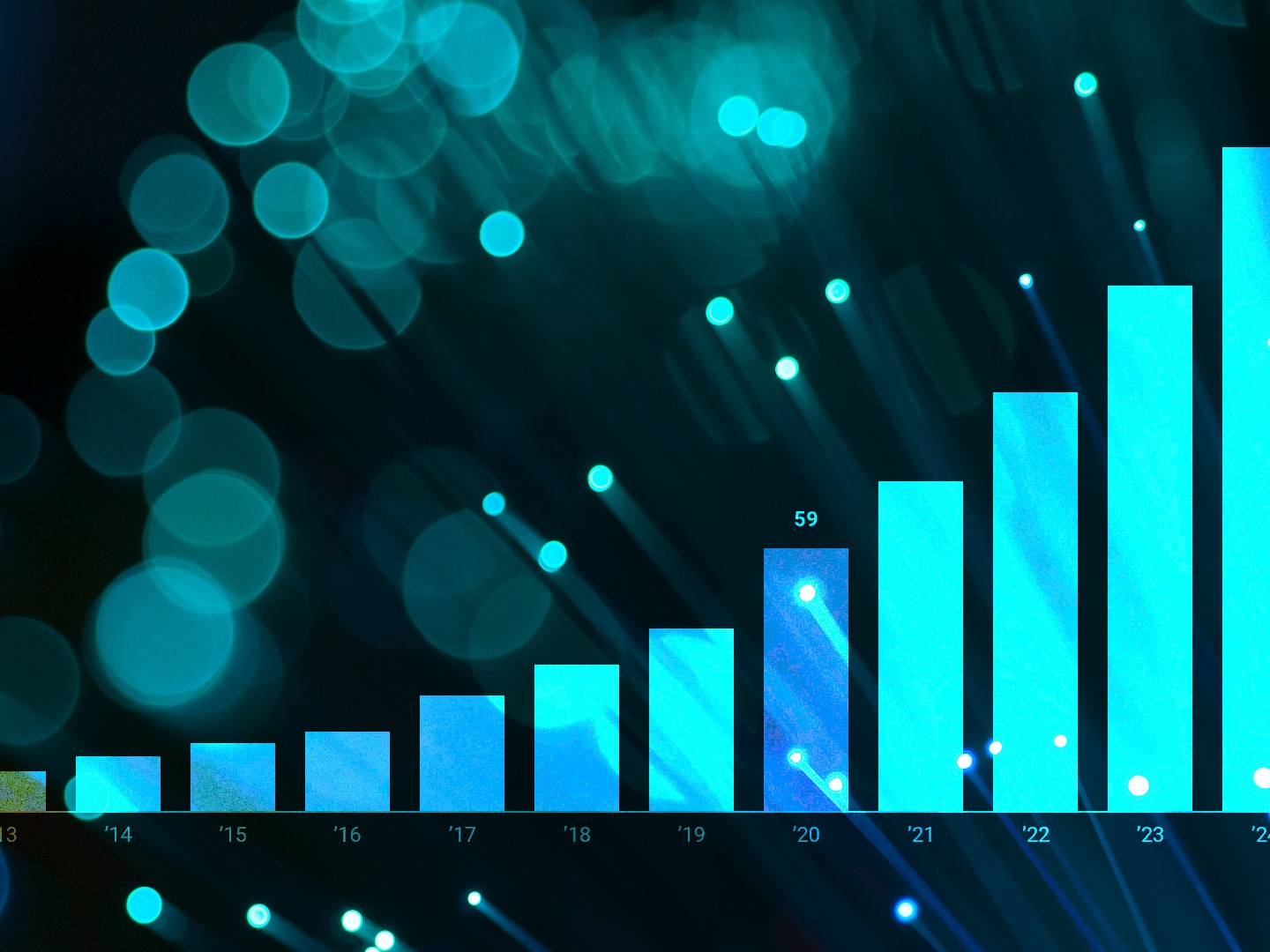
DataSphere Report Factors Pandemic Into Growth Forecast in Latest Update
Sep 9
A new update to IDC’s DataSphere report forecasts continued growth of the world’s created and consumed data with a shifting data landscape impacted by the COVID-19 pandemic. We break down some of the key insights.

Beyond Bytes: Navigating the Names Used to Measure Massive Units of Digital Data
May 20
Gigabytes…Terabytes…Petabytes…Zettabytes… Naming new units of computer memory may be fun but once you venture beyond the volumes we see in our current digital landscape it becomes a bit informal. Keeping track of just how large the numbers are isn’t so easy either. How much big data is there in a Yottabyte?

Apollo Moon-Landing Tapes Expected to Fetch Over a Million in Auction
Jul 16
Three reels of moon-Landing tapes that were bought by an intern 43 years ago for a couple hundred dollars could fetch $1 million at an auction this week.

Black Hole: It Takes Big Data to See The Big Picture
Apr 11
The first-ever image of a black hole was revealed to the world by an international team of researchers from the Event Horizon Telescope (EHT) project in a culmination of years of work, astronomy and computer science feats. How much data must you compute to get an image of something that’s 55 million light-years away, has a mass 6.5 billion times that of our own sun, from a network of 8 telescopes that combine to make a dish the size of the Earth?

Dissecting the Digitization: Data Age 2025
Dec 18
The latest IDC Data Age 2025 whitepaper The Digitization of the World (from Edge to Core) is available now. We’re breaking down some of the key points in the report for you.

Equifax: Zero Credit for Poor Handling of Massive Data Breach
Sep 26
“Based on the information provided, we believe that your personal information may have been impacted by this incident.”
Sound familiar? You and 143 million other people in the United States, the UK, and Canada.That’s right – Americans weren’t the only ones affected by the massive Equifax data breach.
It’s been quite a year for data breaches (many a result of escalating and evolving ransomware), but this situation was largely precipitated by Equifax’s negligence. Companies who feel they are taking extensive preventative measures can always do more. Being on the defense is not the same as mounting an offense.

Paring Down the Data: Data Age 2025
Apr 24
IDC has released a long white paper, Data Age 2025, on the evolution of data in our lives, how we have moved through different eras of data and computing and highlighting key trends today. We break down the main points, talk about it’s new critical nature, and a bit about pizza toppings.

Spring Into Action: Top 5 Do's & Don'ts of Data Cleanup
Apr 19

“April showers bring May flowers,” as they say. April also brings with it the frenzy of spring cleaning. This is the time of year when everything must sparkle, fit neatly into its predetermined spot, or go curbside. Everywhere and everything is fair game: your home, your garage, the interior and exterior of your car, your fridge, your office, and…your data.
Just like the clutter in your closet or garage, your data can be disorganized, old, poor quality, or redundant. Fortunately, de-cluttering your data will make your life (and business) run more smoothly in the long-term.
All We See Is The Code
Sep 27
Unless you have experienced a hard drive failure, you may not be aware of the complexity how data is stored. A CBL data recovery expert sees a string of ones and zeroes organized in a perfect pattern otherwise known as your once-in-a-lifetime trip to Paris. It’s all about perspective.
Happy New Year 2010
Dec 31
We here at CBL would like thank you for selecting us as your data recovery service provider for 2009.
Looking back on another year we were lucky enough to work on many unique projects. Despite the ever changing technology landscape we here at CBL strive to continuously develop and...
Keep a Lid on IT
Feb 5
...resist the temptation to tamper with or hand over the drive to anyone but a professional data recovery specialist…
Can you afford to be without your data?
Jan 14
Hard drives don’t discriminate. Whether the economy is in a recession or a boom, no one is immune to data loss. It’s never a matter of IF data loss will happen; it’s simply a matter of WHEN.

Save Data. Dispel Data Recovery Myths.
Oct 29
Data recovery is not simple or straightforward. Data loss can occur for numerous reasons. Just as numerous are misconceptions about the data recovery process.
Aftermath of Hurricane Ike - Data on Storm-Damaged Computers May Be Recoverable
Sep 15
As residents of the Greater Houston Area begin the cleanup after Hurricane Ike’s devastation, consumers and business owners alike who discover storm- and water-damaged computers in their homes and offices should follow this advice.
If you have family or friends in the Houston area, let them know they can...
Heads and Tales: For 24 hours, CBL is THE Hub
Dec 6
For 24 hours, CBL is THE Hub.
Canada’s data recovery specialist comes to hubcanada.com’s rescue.
For small business owners, the end of the business day rarely finishes at five o’clock. In fact, taking work home to complete or review at the end of the day or on the weekend has...
When a backup drive is not a "backup"
Nov 28
Many times we get customers who bring in their external drives just after a crash. Often the external drive is referred to as their “backup”.
“I copied all of my data to my backup and it failed …”
Well, what about your original data? You mean this was your only copy?...

Rare Music Files Rescued from Severely Damaged Hard Drive
Nov 5
Heads and Tales: Out of the Ashes
When vintage music store, M.C. Productions Vintage Recordings, Penticton, British Columbia, Canada was destroyed in a fire, owner Mickey Clark lost all of the CDs he had compiled from his massive record collection, all of the backup disks from the music files he had digitized, and half of his inventory of 20,000 original recordings dating back to 1902. In addition, both of his hard drives were drowning in two feet of water. To the distraught performer, that meant the possible loss of thousands of music files many of which were Clark’s only copies which he started collecting at the age of eight.
Protecting Your Data From Identity Theft
Oct 4
Identity theft doesn’t just happen when somebody sorts through your garbage or steals your wallet. Thieves can steal your digital identity as well.
Like many of us in the technology field (or even the home user) we’ve accumulated several PC’s which are no longer used. Wait! Before you decide to trash...